How it started
When WannaCry hit, the news sent shivers down the world. Reports of hospital outages and super secret tools used by the NSA (Equation Group) that could hack into any version of Windows was released to the public. During this period of time, the community warned of more waves were soon to come. This started at June 26, 2017 primarily in Ukraine and Binary Defense started to see some of the first large infections of Petya (or some calling it NotPetya) happening at other geographic locations early this morning. On the surface, this appeared to be another EternalBlue/MS17-010 campaign being used on the surface and a new variant. No-one at the time knew exactly how the infection methods were being used, but multiple companies jumped the gun and reports claimed multiple avenues including HTA attack vectors, email campaigns with attached word and excel documents.
So What Really Happened?
A third party software called M.E. Doc (MeDoc) which, is an accounting software primarily used in the Ukraine was compromised. With any of these early warning signs, there is a lot of information and data to cut through before actually coming to a factual conclusion. Other vectors such as documents, excel, and obfuscated HTA’s seem to be confused reports on another campaign called the Loki Bot. Based on the analysis, if any organization had MeDoc installed, they would be impacted as soon as it was updated. MeDoc is a required software out of Ukraine – so there was a large footprint here from Ukraine-based companies and orgnaizations that do business in Ukraine. There is substantial evidence supporting this as the main method and has been confirmed by multiple organizations including Binary Defense.
Why Everyone Freaked?
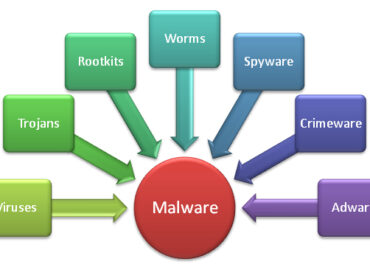
Unlike WannaCry, Petya used multiple techniques in order to compromise hosts in a very fast timeframe. The first technique was using the EternalBlue (MS17-010) exploit. While this was occurring, other scenarios happened on the system:
1. An older version of psexec v1.98 is dropped onto the system under C:\Windows\dllhost.dat. Why the version is important is that in version 2.1 of psexec, encryption was introduced for credential authentication. If monitoring command line arguments in v1.98, you can see the clear-text passwords for authentication in this specific variant (good indicator of actual accounts that were used and the passwords compromised).
2. A technique used by Mimikatz and other tools leveraging lsadump to dump passwords from memory is used in order to extract clear-text passwords from memory. These are parsed, and then used by WMIC and PSEXEC. We can clearly see clear-text passwords being used when executing the WMIC and PSEXEC command line.
3. PSEXEC and WMIC are used in order to attempt to spread across the network using the extracted credentials. For both PSEXEC and WMIC methods to work, the ADMIN$ hidden share needs to be exposed and successful authentication in order to connect to the remote system.
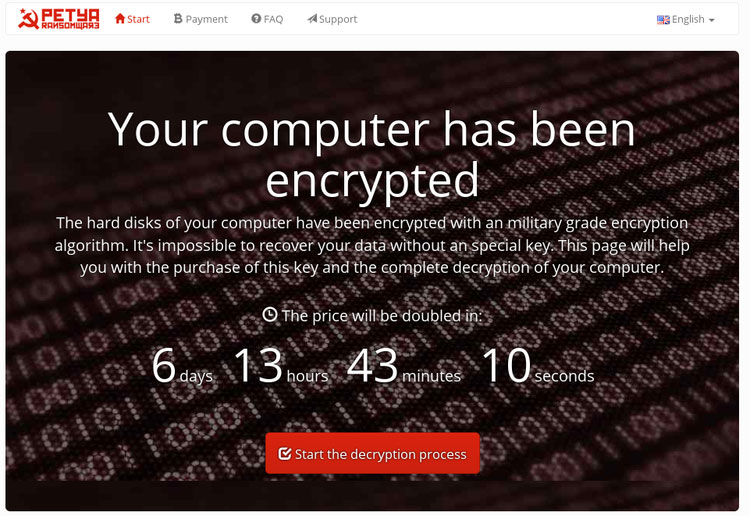
Do not pay the ransom!
Since the time of the ransomware, the email address (wowsmith123456 [at] posteo.net) that was used to contact for the recovery key was suspended and recovering the files is not possible (at this time). This means do not pay the ransom.
How to Protect
Most major antivirus companies now claim that their software has updated to actively detect and protect against “Petya” infections.
Is Petya related to WannaCry?
Petya also uses the ETERNALBLUE exploit, also used by the otherwise unrelated WannaCry ransomware worm in mid-May, to spread among Windows machines in an enterprise network. If an enterprise server, or even any Windows computer, has specific network ports – in this case, ports 139 and 445 – open to the internet, then Petya could use that opening to infect the entire local network.
If you have any questions, please email to [email protected]